How Does a Crypto Wallet Work? The Complete 2026 Guide
Understanding how a crypto wallet works is one of the most important steps you can take as a crypto user. Millions of people hold cryptocurrency today. Yet very few truly understand the technology behind their cryptocurrency wallet. That gap in knowledge costs people money sometimes everything they own in digital assets.
This guide breaks it all down. You will learn what is a crypto wallet, how it protects your funds, the different types available, and how to keep your assets safe. Whether you hold Bitcoin, Ethereum, or any other digital asset, this guide is for you.
The global crypto wallet market was valued at $12.20 billion in 2025. It is projected to reach $98.57 billion by 2034, growing at a rate of 26.7% per year. Over 820 million active users now hold a digital wallet crypto solution worldwide. That is roughly 15% of all internet users on the planet.
The demand is clear. The need to understand it properly is even clearer.
Table of Contents
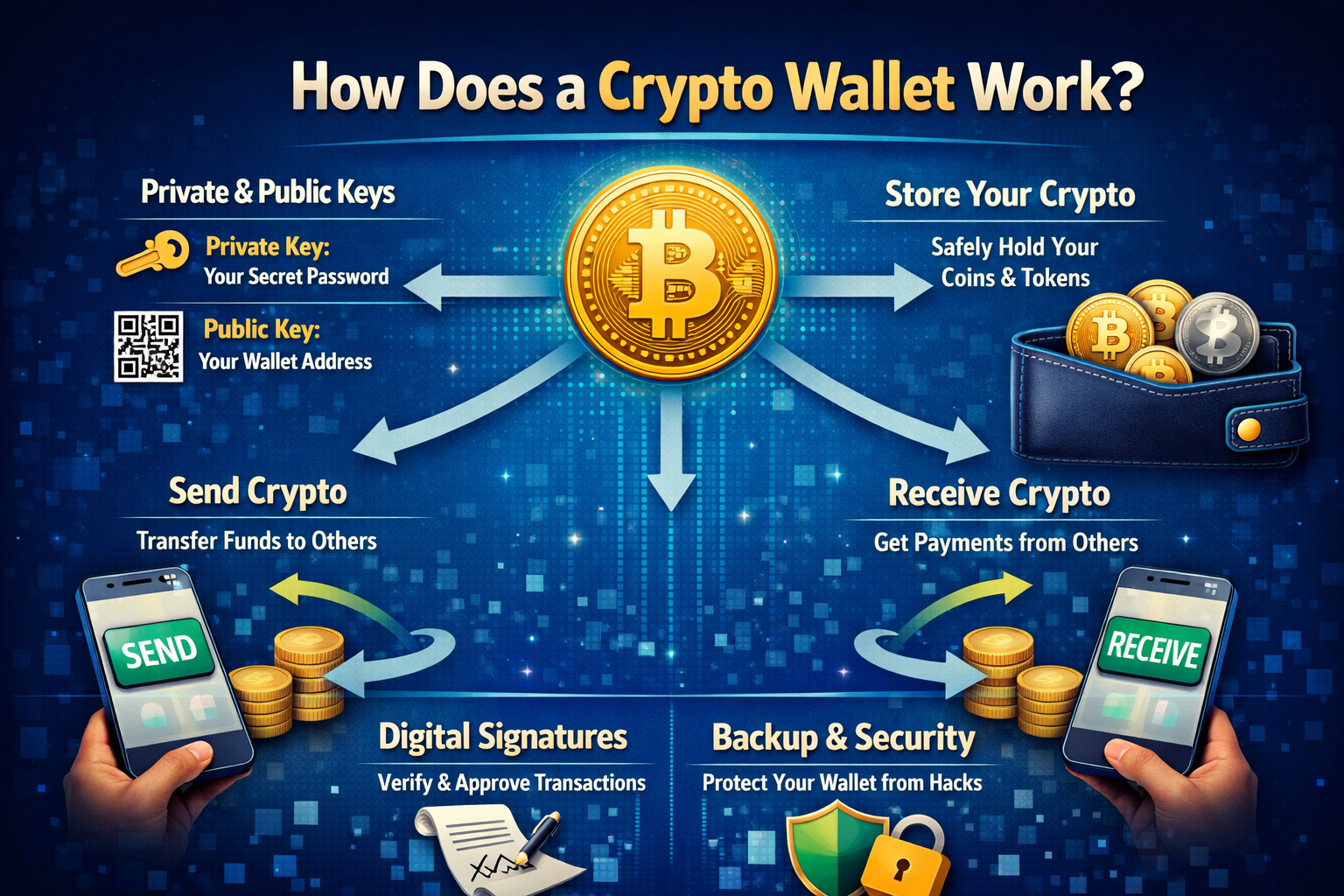
What Is a Crypto Wallet and What Does It Actually Store?
A crypto wallet is not what most people think it is. It does not hold your coins. Your Bitcoin, Ethereum, or any other digital currency never leaves the blockchain ledger. It always lives there permanently.
What a cryptocurrency wallet stores are your cryptographic keys. These keys prove that you own the funds recorded against your address on the blockchain. Without those keys, you cannot access or move a single coin, no matter how much is sitting there.
Think of it like this. The blockchain is a massive public record. Your wallet holds the proof of identity that lets you update your entry on that record. Lose the proof, lose everything.
This is why crypto ownership control rests entirely with you. There is no bank. There is no helpline. You are your own financial institution.
How Crypto Wallets Work: The Cryptographic Key System
Every blockchain wallet on earth runs on the same foundation: a system called asymmetric cryptography. This is what makes crypto wallet security so powerful. Here is how it works.
What Is a Private Key in Crypto?
When you create a wallet, the first thing generated is your private key crypto credential. This is a randomly produced string of 256 bits, essentially a number so large it is impossible to guess. It functions as the master password to your funds.
Your private key does one job: it signs and authorises every outgoing transaction you approve. The signature proves you own the wallet without ever revealing the key itself. Private key protection is the single most important security task in crypto. Whoever has your private key has your money permanently and irrevocably.
What Is a Public Key in Crypto?
From your private key crypto credential, your wallet mathematically generates a public key crypto identifier. This uses a one-way mathematical process called elliptic curve multiplication. You can derive a public key from a private key easily. Going the other direction, finding the private key from the public key is computationally impossible with current technology.
Your public key is safe to share. The network uses it to confirm that your digital signature crypto on a transaction is genuine and authorised by you.
What Is a Crypto Wallet Address?
Your crypto wallet address is derived from your public key through an additional hashing process. This is the string of characters you share when someone needs to send and receive crypto with you similar to a bank account number.
Your address is completely public. Anyone can see it on the blockchain. But only the person holding the matching private key can authorise any outgoing transaction from it.
The relationship works like this:
| Component | Role | Can Be Shared? |
| Private Key | Signs and authorises transactions | Never |
| Public Key | Verifies your identity on the network | Yes |
| Wallet Address | Receives incoming crypto | Yes |
How a Crypto Transaction Actually Works: Step by Step
Understanding crypto transactions from start to finish removes all the mystery. Here is exactly what happens every time you send and receive crypto.
Step 1: You Initiate the Send
You open your crypto wallet app and enter the recipient’s crypto wallet address along with the amount. Your wallet constructs a transaction message with all relevant data.
Step 2: Digital Signing Takes Place
Your wallet uses your private key to produce a digital signature crypto for that specific transaction. This signature is mathematically unique to this exact transaction. It cannot be reused or forged. Signing transactions is how crypto ownership control is proven without exposing the key.
Step 3: Broadcasting to the Network
The signed transaction is broadcast across thousands of nodes on the peer-to-peer network. This is part of how blockchain interaction works at its core.
Step 4: Transaction Verification
Nodes across the network check two things: that the digital signature crypto is valid, and that the sending wallet has sufficient funds. This entire transaction verification process happens without anyone ever seeing your private key. That is the elegance of cryptographic keys.
Step 5: Confirmed on the Blockchain
Once verified, the transaction is added permanently to the blockchain ledger. It is irreversible. There is no undo, no dispute, and no customer service. Manage crypto assets carefully every confirmed transaction is final.

What Is a Seed Phrase and Why Does It Matter?
Modern wallets use a system called Hierarchical Deterministic (HD) architecture. This generates an entire family of key pairs from one master seed. This is how a single wallet can manage crypto assets across Bitcoin, Ethereum, Solana, and dozens of other chains simultaneously.
The readable form of this master seed is your recovery phrase also called a seed phrase. It is a sequence of either 12 or 24 random words drawn from a standardised list. This is defined by the BIP-39 protocol.
Your seed phrase is your entire wallet. Whoever has those words controls every account, every balance, and every asset your wallet has ever generated.
A 24-word wallet backup method offers approximately 2²⁵⁶ possible combinations. That number exceeds the atoms in the observable universe. The mathematics is unbreakable. Human behaviour is not.
Wallet backup methods must always start here. Write your seed phrase on paper. Store it physically. Never photograph it. Never type it into anything except your own wallet during account recovery.
Types of Crypto Wallets Explained
Not every crypto wallet suits every purpose. Choosing the right type depends on your habits, your holdings, and your appetite for responsibility.
Hot Wallets vs Cold Wallets: The Core Distinction
The most important dividing line in the wallet world is hot wallet vs cold wallet. Hot wallets are internet-connected. Cold wallets are not. That single difference drives almost every security trade-off.
Hot wallets account for 78% of all crypto wallets in 2025, according to CoinLaw research. They dominate because of their accessibility. They are free, fast, and ideal for regular crypto transactions. The downside is that constant blockchain interaction through an internet connection creates exposure to attacks.
Cold storage crypto keeps your cryptographic keys entirely offline. Hardware devices like Ledger and Trezor connect to the internet only when you physically approve a transaction. Hardware wallet sales rose 31% in 2025, driven by growing security awareness. These devices represent the gold standard for protecting serious holdings. Cold wallets make up 22% of usage in 2025, with significant uptake among long-term investors.
Software Wallet Crypto (Hot Wallets)
A software wallet crypto solution comes in three main forms.
A mobile crypto wallet like MetaMask Mobile or Trust Wallet runs as a smartphone app. MetaMask alone reports over 30 million monthly active users in 2025. Mobile wallets account for the majority of daily usage worldwide. Over 58% of users demand mobile wallet access as of 2025. Trust Wallet grew installations by 40% year-on-year in 2025.
A desktop crypto wallet like Exodus or Electrum runs as installed software on your computer. It gives more control and is suited to managing larger, more complex portfolios. However, it remains internet-connected and therefore subject to the same threats as other hot wallets.
A browser wallet like MetaMask for Chrome or Brave connects directly to decentralised finance (DeFi) platforms and Web3 wallet access points. It is the primary tool for anyone interacting with dApps and NFT marketplaces. Browser extensions make up around 12% of total wallet usage in 2025.
Hardware Wallet Crypto (Cold Wallets)
A hardware wallet crypto device is a physical product typically resembling a USB drive that stores your private key crypto credential offline at all times. The device connects briefly only when you are ready to approve a transaction. Your keys never touch an internet-connected environment during normal use.
This design makes hardware wallets immune to remote attacks. Even malware on your computer cannot extract the keys because they never leave the device. Cold storage crypto at this level is the recommended solution for any holding you would genuinely struggle to lose.
The hardware wallet segment reached $0.56 billion in 2025 and is projected to hit $2.06 billion by 2030.

Paper Wallet Crypto
A paper wallet crypto solution is a physical printout of your public and private keys, often represented as QR code crypto payments codes. Generated correctly on an offline computer, it is fully immune to digital attacks. However, it is fragile, impractical for regular use, and vulnerable to physical loss, fire, or water damage.
Custodial vs Non-Custodial Wallet: The Most Critical Choice
This distinction cuts across every wallet type. It is the most important choice any crypto user makes.
A custodial wallet is managed by a third party typically a crypto exchange wallet like Coinbase or Binance. They hold your cryptographic keys on your behalf. This is convenient but means you are trusting the platform entirely. Custodial wallets are used by 41% of users in 2025.
A non-custodial wallet means you hold your own keys. Full ownership. Full responsibility. Non-custodial wallets are preferred by 59% of users in 2025, reflecting a shift toward self-sovereignty. Self-custody awareness has risen to 71% among crypto users in 2025 according to CoinLaw data.
The collapse of FTX in 2022 wiped out billions in customer funds and remains the defining lesson in custodial risk. The community principle is simple and absolute: “Not your keys, not your coins.”
Multisignature Wallets
A multisignature wallet requires multiple cryptographic keys to authorise any transaction. A common setup is 2-of-3 any two of three designated keys must sign. This eliminates the single point of failure inherent in standard wallets and is increasingly used for DeFi wallet integration, business treasury management, and estate planning. 36% of enterprises now require shared custody solutions of this kind.
Multi-Chain Wallet and Web3 Access
A multi-chain wallet allows users to hold and transact across multiple blockchains from a single interface. In 2025, the average DeFi wallet supports 5.4 tokens and interacts with 2.3 chains. DeFi wallet integration and Web3 wallet access have become standard expectations. 48% of all wallets in 2025 have interacted with at least one decentralised application.
How to Secure Your Crypto Wallet: Essential 2025 Rules
The mathematics protecting crypto wallets is essentially unbreakable. The human behaviour around them is frequently not. These security rules are non-negotiable.
Protect Your Seed Phrase Above All Else
Your seed phrase is the most important piece of information in your financial life. Write it on paper immediately after creating your wallet. Store copies in at least two separate secure physical locations. A fireproof home safe and a bank safety deposit box is a solid approach. Never photograph it. Never type it into any website or form. Never share it under any circumstances including requests from people claiming to be technical support.
Never Store Seed Phrases Digitally
Wallet backup methods must be physical. Cloud storage, email, notes apps, and password managers are all inappropriate for seed phrase storage. Digital copies can be accessed remotely. Paper cannot. For permanent long-term backup, consider engraving your phrase onto a fireproof steel plate.
Use Hardware Wallets for Significant Holdings
Any amount of crypto whose loss would cause you serious hardship belongs in cold storage crypto. The cost of a quality hardware wallet typically between £80 and £200 is negligible compared to the protection it provides.
Use Authenticator Apps, Not SMS, for 2FA
Two-factor authentication crypto is mandatory on every custodial wallet and crypto exchange wallet account you hold. However, SIM-swap fraud remains a significant attack vector in 2025. Avoid SMS-based 2FA entirely. Use an authenticator app or a hardware security key instead.
Verify Every Wallet Address Before Sending
Clipboard-hijacking malware silently replaces copied wallet addresses with attacker-controlled ones. Before confirming any transaction, manually verify at minimum the first and last six characters of the destination crypto wallet address.
Stay Alert to Evolving Phishing Attacks Crypto
Phishing attacks crypto scammers use are growing more sophisticated every year. AI-generated messages and deepfake voice calls impersonating support staff are now commonplace. No legitimate wallet provider, exchange, or support team will ever ask for your private key crypto or seed phrase under any circumstances. If someone does, it is a scam.
Frequently Asked Questions About Crypto Wallets
What is a crypto wallet in simple terms? A crypto wallet is a tool that stores your cryptographic keys the credentials that prove you own funds on a blockchain. It does not store coins directly. Your assets always live on the blockchain ledger, and your keys are what give you access to them.
Can a crypto wallet be hacked? The cryptographic keys system itself has never been broken. However, phishing attacks crypto actors target human behaviour. If you reveal your seed phrase or store your private key digitally, your wallet can be compromised. The math is secure. The habits matter most.
What happens if I lose my crypto wallet? If you have your seed phrase, you can fully restore your wallet on any compatible crypto wallet app at any time. If you lose both your device and your recovery phrase, the funds are gone permanently. No one can recover them.
What is the difference between a hot wallet and a cold wallet? A hot wallet vs cold wallet comparison comes down to internet connectivity. Hot wallets are always connected, making them convenient but more exposed to attack. Cold storage crypto via a hardware wallet keeps your keys offline, providing far greater security for significant holdings.
What is the safest type of crypto wallet? For maximum protection, a hardware wallet from a reputable manufacturer is the gold standard. For everyday use and DeFi wallet integration, a reputable non-custodial wallet with careful seed phrase management offers strong security without sacrificing usability.
What is a seed phrase and why is it important? A seed phrase also called a recovery phrase is a sequence of 12 or 24 words that represents your entire wallet. It is the only way to recover your accounts if you lose access to your device. It must be stored physically, never digitally, and never shared with anyone.
Conclusion: Take Control of Your Crypto
Understanding how a crypto wallet works is the foundation of safe, confident participation in the digital asset space. Your private key crypto credential proves your ownership. Your seed phrase backs everything up. Your wallet encryption and security habits determine whether it stays protected.
The crypto wallet market is growing at extraordinary speed. Software wallet downloads surpassed 520 million globally in 2025. More than $250 billion in digital assets are now held in non-custodial wallets worldwide. The infrastructure is maturing. The responsibility to understand it has never been greater.
Choose the right wallet type for your needs. Protect your cryptographic keys with the seriousness they deserve. Whether you are exploring decentralised finance (DeFi), holding Bitcoin long-term, or discovering Web3 wallet access for the first time start with security. Everything else follows from there.
Ready to take full control of your digital assets? Start by choosing a non-custodial wallet, securing your seed phrase offline, and never trusting anyone who asks for your private key.
Disclaimer: This article is for educational purposes only. It does not constitute financial or investment advice. Cryptocurrency involves significant risk. Always conduct your own independent research before making any investment decisions.

 Bitcoin
Bitcoin  Ethereum
Ethereum  Tether
Tether  XRP
XRP  USDC
USDC  Solana
Solana  TRON
TRON  Lido Staked Ether
Lido Staked Ether  Figure Heloc
Figure Heloc  Dogecoin
Dogecoin  WhiteBIT Coin
WhiteBIT Coin  Hyperliquid
Hyperliquid  USDS
USDS  Zcash
Zcash  Wrapped stETH
Wrapped stETH  LEO Token
LEO Token  Cardano
Cardano  Wrapped Bitcoin
Wrapped Bitcoin  Bitcoin Cash
Bitcoin Cash  Binance Bridged USDT (BNB Smart Chain)
Binance Bridged USDT (BNB Smart Chain)  Monero
Monero  Chainlink
Chainlink  Canton
Canton  Toncoin
Toncoin  Wrapped eETH
Wrapped eETH  Stellar
Stellar  USD1
USD1  MemeCore
MemeCore  sUSDS
sUSDS  Ethena USDe
Ethena USDe  Dai
Dai  Coinbase Wrapped BTC
Coinbase Wrapped BTC  Sui
Sui  Litecoin
Litecoin  Avalanche
Avalanche  WETH
WETH  Hedera
Hedera  Rain
Rain  PayPal USD
PayPal USD  USDT0
USDT0  Shiba Inu
Shiba Inu  Cronos
Cronos  Circle USYC
Circle USYC  Global Dollar
Global Dollar  Tether Gold
Tether Gold  BlackRock USD Institutional Digital Liquidity Fund
BlackRock USD Institutional Digital Liquidity Fund  Bittensor
Bittensor  Ethena Staked USDe
Ethena Staked USDe 




